The Mining Bird
Greetings, Special Agent K.
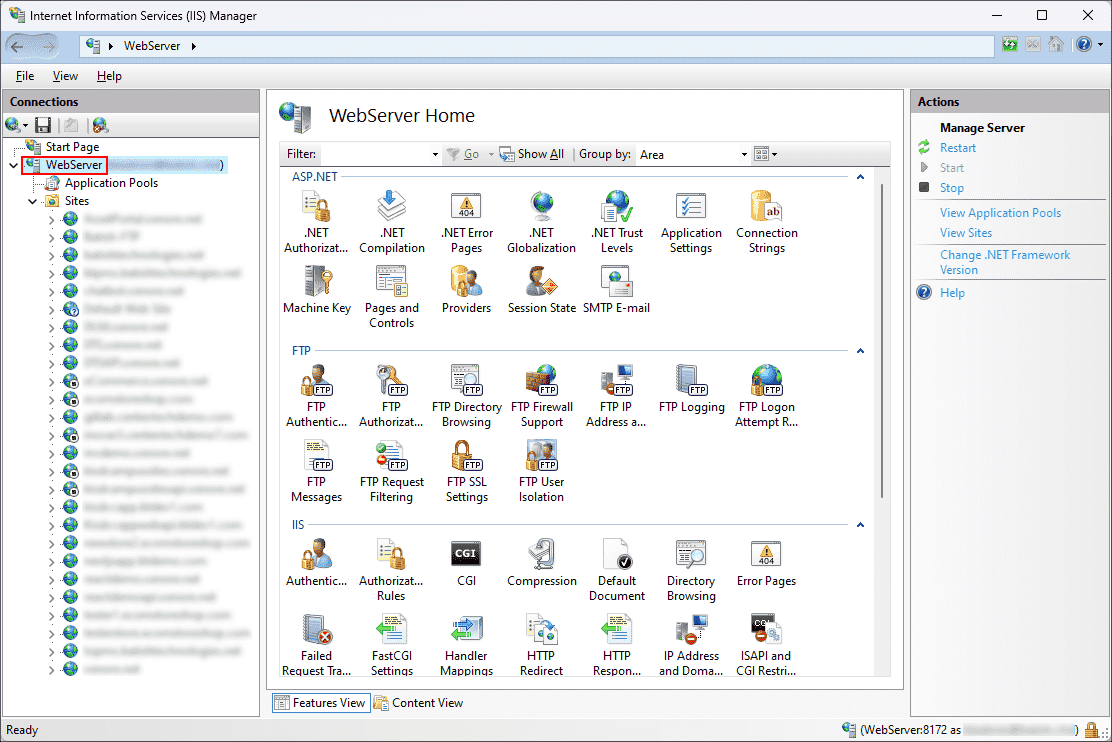
The client has identified a massive compromise across their IIS server farm. The malicious activity is characterized by abnormal CPU spikes dedicated to cryptocurrency mining. While the firewall failed to block the outbound traffic, the detection system (SIEM/EDR) triggered a critical alert based on a suspicious sequence of Windows events.
The attack follows a logical progression of Access Token Manipulation to achieve elevation of privileges:
- Event ID 4624 : A successful logon session was created. The attacker leveraged a web service account previously compromised through a web application vulnerability.
- Event ID 4688 : This is where the elevation occurs. The attacker executed an impersonation tool (obfuscated as let.exe) to transition from "Service" status to NT AUTHORITY\SYSTEM. Command used : "C:\programdata\let.exe -t t -p c:\programdata\rn.bat -l 1234 -c {8BC3F05E-D86B-11D0-A075-00C04FB68820}"
We are concerned this breach goes deeper than simple mining. We urgently need to attribute this activity to a specific threat actor and pinpoint the exact mechanism they exploited to escalate their privileges.
To validate your incident report, you must provide the following:
- The unique Group ID on the MITRE ATT&CK framework.
- The technical name of the Windows Privilege abused to achieve this escalation.
As always, Special Agent K, the contract is yours, if you choose to accept.
Answer Instruction
Download the flag-file using the button below
Unlock the flag-file using the answer as the password
Answer format: MitreGroupID-PrivilegeUsed
Answer example: G0206-SeDebugPrivilege